| atk > documentation > help > starting an attack | Last update: 2004/11/06 by Marc Ruef |
Starting an Attack
The Attack Tool Kit is a security scanner and exploiting framework. It is possible to detect potential flaws and to exploit found vulnerabilities. Please keep in mind that you should never scan a ressource without permission of the owner nor administrator.
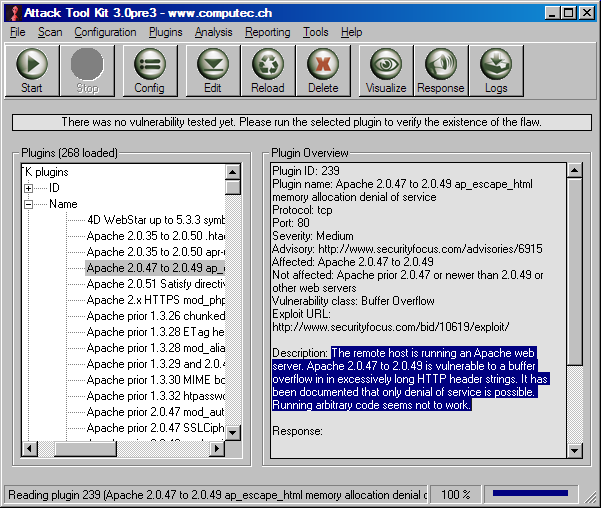
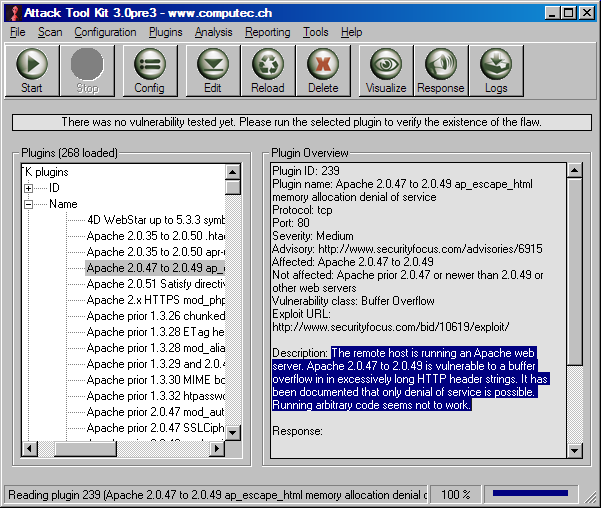
After starting the application and modification the configuration, you have to select a plugin you want to run. This can be done by expanding the plugin tree in the main frame and clicking on your desired check. The plugin will be highlighted, read from the file and loaded into the RAM memory. On the main frame you can see the plugin overview that is the content of the loaded plugin. Read the description to learn what this check will do. If this is what you are looking for, you are able to start the attack.
There are different ways to start the attack of the selected plugin. First of all you have to know that every ATK plugin since ATK 3.0 has two different attack procedures. The detection procedure is able to detect a vulnerability without exploiting it. In most cases active banner-grabbing is used to determine vulnerable versions of checked applications. This is a very quick and less dangerous way. On the other hand the exploiting procedure is able to exploit the defined vulnerability. This is more accurate, often longer and more dangerous, because the exploitation of a flaw may affect the running system.
If you are doing a first enumeration of potential flaws, for example in a simple security audit, start the detection routine. This can be done by clicking the right mouse button after selecting a plugin. The plugin context menu shows the run entry. Select the child entry detection if available and the detection procedure starts. On the other hand if you are interessted in exploiting a potential vulnerability, for example to determine the real existence of a flaw or to realize a penetration test, select the exploit routine instead. The exploit procedure will run. If you are interessted what is going on during an attack, open the Attack Visualizer or Log frame.
After the check has finished, the ATK shows you the result. In the top of the main frame a short message can be found. This note indicates wheter the detection or exploitation of vulnerability was successfull or not. Now you are also able to make further analysis of the finished attack and the gathered information. This can be done by opening the Attack Response by clicking on the colored message or the response icon.
If you are not happy with the results or you want to change the behavior of a plugin, open the Attack Editor.
When you have finished your vulnerability scan with the ATK and you were able to detect a flaw, do not forget to realize adequate countermeasures. A security audit without solutions is worthless.